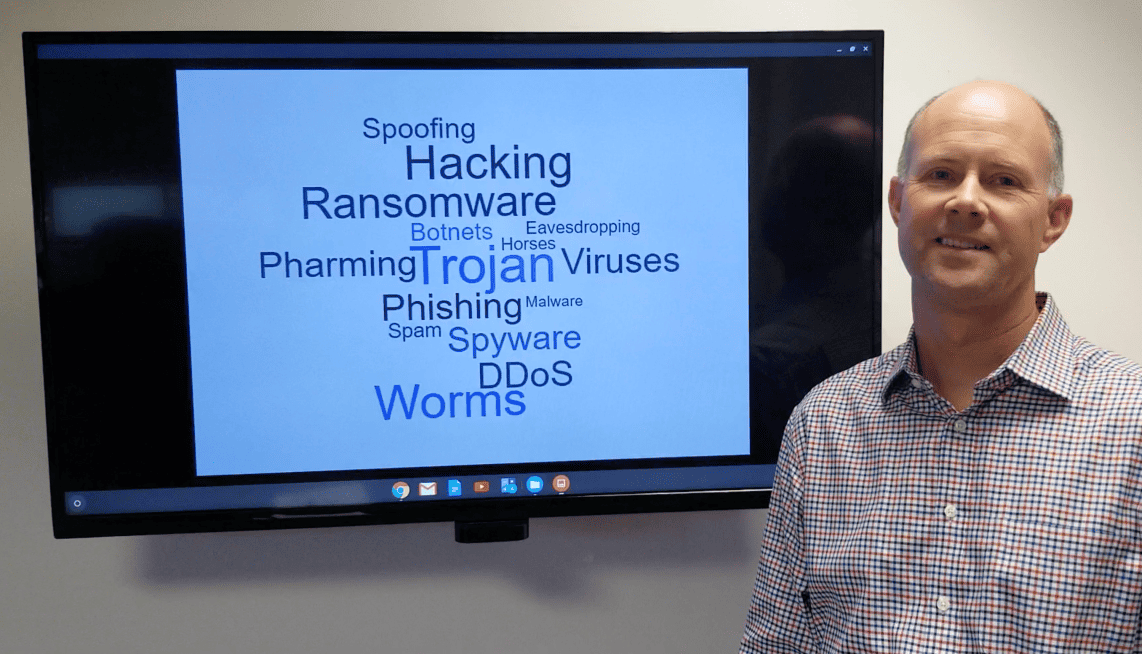
Cyber security is a real threat. Those who have ill-intentions use advanced techniques to lure unsuspecting people into a trap. While your personal data will remain at risk, cyber education and ongoing diligence can prevent many problems. Cornerstones of cyber security include people, passwords, personal devices, updated software, and outside companies.
The first four items are totally within your control. Using self-awareness, strong passwords, and ensuring that your personal devices (phones, laptops, etc.) have the most current operating systems and antivirus software will help keep you safe. Passwords should be strong – minimum of 10 characters utilizing upper and lower case letters, numbers, and special characters. Try to change your password every 90 days. If you have lots of passwords, consider using a password management app. Likewise, ensure popup blockers are turned on, don’t conduct any business via free WiFi connections, and only transmit private data via secure website links (those beginning HTTPS://). All devices should require a secure password, face scan, or biometric data for access. Never leave your device open/unattended.
When your data is housed with an outside companies, you’re pretty much relying on them to have secure practices. The numerous and significant breaches reported in the news show that even with safeguards in places, hackers are one-step ahead/willing to exploit the smallest flaw. In many cases, access is granted when an unsuspecting employee opens the door via an email link, attachment, or pop up. Even if these items look valid, if you’re not 100% sure, you should check before you click. This includes verifying the sender’s email address, checking the name of the attached file/type vs. known/expected file types, and checking the URL (web address) of a link prior to clicking (you can often do this by hovering your mouse over the link). If something looks off, stop and get additional help to further verify.
A current scam involves a call from “Apple Support” regarding a security issue requiring your attention. The first red flag with this scam is that entities like Apple, Microsoft, Dell, etc. will not call you if there’s an issue. Consider the size/scope of their clients…calling out is not in the cards. If you get a call/message, ignore it! Never call back to a number provided. Should you wish to call/confirm what’s going on, do an independent search for the support number of the company that supposedly called you. Odds are, it’s different.
Those who act on the support call are instructed to input a web address so that the technician can “help.” This is red flag #2 – never input the address provided by the caller. When using support options, search for the address yourself/link to the support site via the main (valid) company site. For those who follow along, the next step involves being sent a code to allow the “support” rep to help “fix” your problem (which is about to get bigger). Once you’ve input that code, the rep then downloads software to your machine to provide “assistance.”
Unfortunately, at that point, Pandora’s box has been opened. The cyber criminal now has full access to your device. The software installed to “fix” your problem, may contain a virus that may creep up in the coming days. If/when it does, you may then become subject to ransomware….where you now have to pay the same company for more “support.” If you don’t take action, your device can be locked out and all your data frozen. In other cases, malware (malicious software) may be installed allowing your personal data to be accessed, passwords copied, spam to be sent via your email, keyloggers installed that record everything you type (like your banking and credit card access), and more.
The best solution is not to click or call back. If you do act/become a victim, shutdown your computer and ensure you’re disconnected from the internet/shared computers. If you’re at work, notify your IT department/person immediately. If you’re at home, using reputable anti-malware software scour your machine may help. The roots of malware are deep…into system files and registry entries, so it’s far more complicated than removing the software the agent installed. Any missteps in the removal process can either leave the malware active or result in your device not functioning. Using professional help to get your machine fixed may be necessary. In extreme cases, all data may be lost, and a new install of your operating system may be required. In that case, having a solid back up of your data is key. Be safe!